Foreword
iOS implants are rare! This is why I didn't wait to read all the publications about it and really enjoyed the hands-on video by Christopher Lopez. But after watching it, I was even more curious about other components of the iOS spyware. I looked at the Symbols in Binary Ninja and found a class called CameraEnabler. Since then, I've been investigating it. Three weeks later, here's the first part of it. I hope you'll enjoy it.
Introduction
What is Predator?
Predator is a sophisticated iOS spyware attributed to Intellexa/Cytrox, deployed against journalists, activists, and political figures between 2021-2023. While excellent analyses from Amnesty Tech, iVerify, and Google TIG have documented the what and why, this series focuses on the how: the internal mechanics that enable this surveillance capability.
What This Article Covers
How the malware initializes its control server after initial compromise
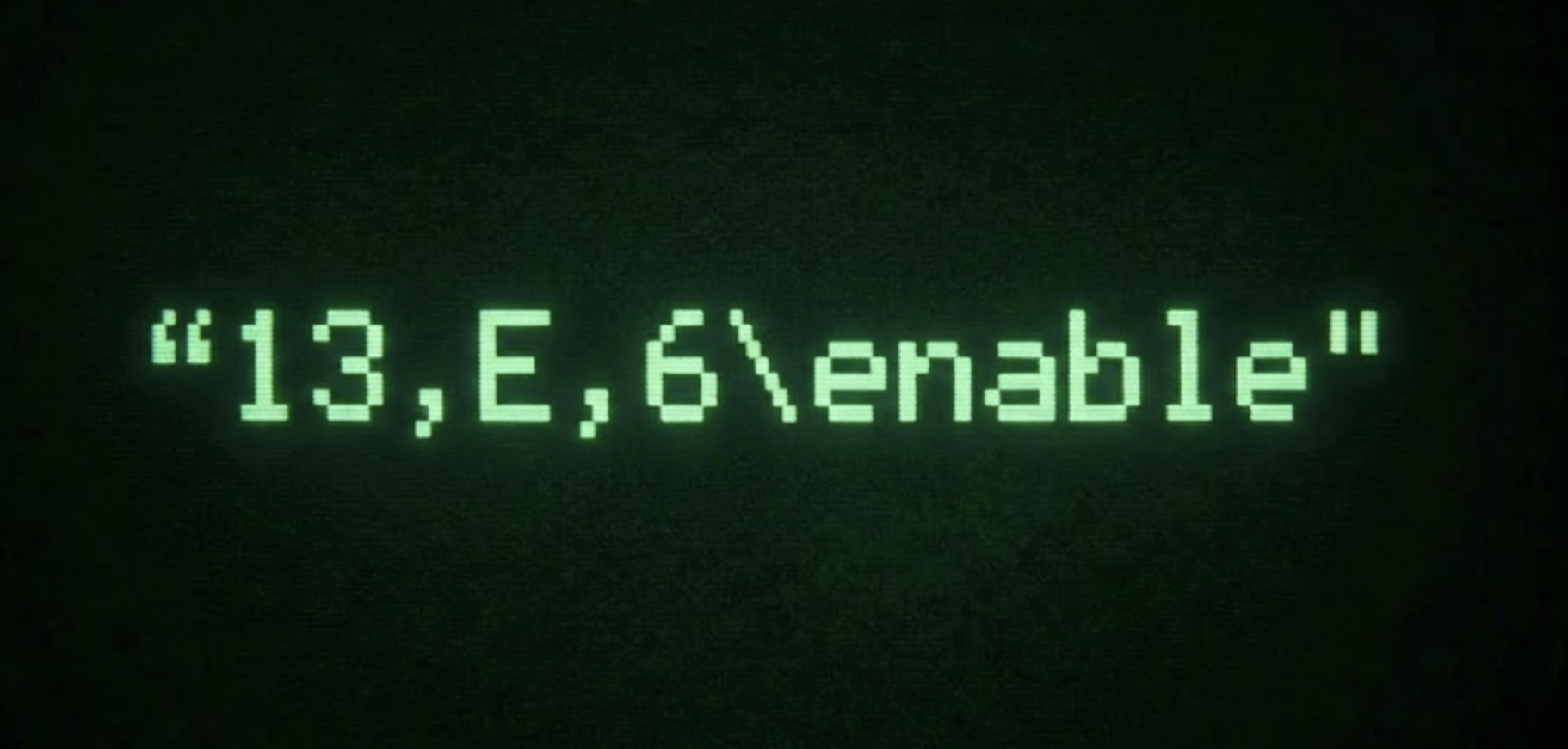
The Unix socket-based IPC mechanism for receiving commands
The factory pattern used to create surveillance modules on-demand
How operations are managed, cached, and destroyed
Notes for the reader
Assembly code is provided as evidence; AI-generated pseudo-code is used for clarity.
Non-essential assembly snippets were omitted for brevity.
Some claims are hypotheses (especially regarding C2 orchestration) and should not be taken as definitive.
Conclusions are presented before proofs to improve readability.