TL;DR: Using our research tool, we discovered that WhatsApp is silently implementing fixes for device fingerprinting privacy vulnerabilities. While the fix remains incomplete, it signals WhatsApp is finally starting to address vulnerabilities that were responsibly disclosed by the security community.
Meta’s WhatsApp, the world’s most popular messaging app with over 3 billion monthly active users, serves as a primary attack channel for cyber attackers seeking to infect victims with malware.
While WhatsApp’s End-to-End Encryption (E2EE) protocol protects message confidentiality, its design and implementation flaws expose users’ device details. This information provides attackers who use WhatsApp as an attack vector with crucial reconnaissance data about potential victims.
Recently, WhatsApp started to silently remediate some of these issues. In this blog post, we will analyze and assess this fix.
The Original Issues
Why fingerprinting matters
When advanced attackers set out to infect their victim’s mobile device with malware, WhatsApp is their main vehicle due to its ubiquity.
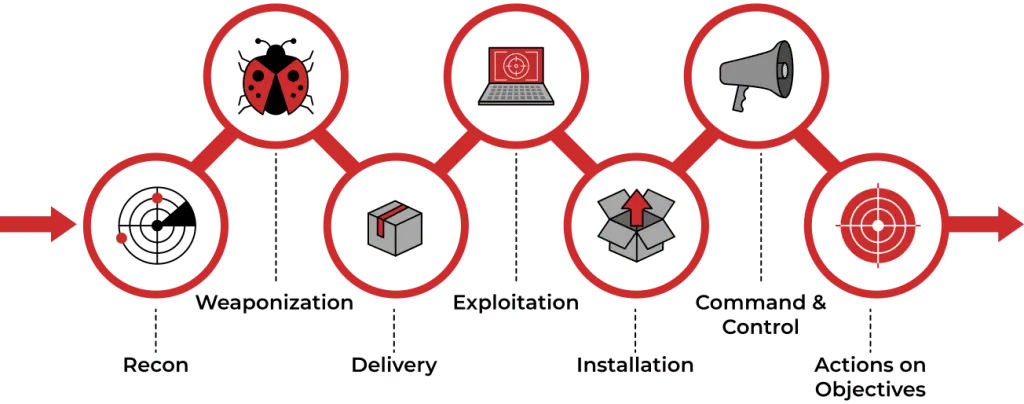
The first step in a cyber campaign is reconnaissance. Attackers must know their victim’s device operating system to successfully infect it. Sending an Android exploit to an iPhone (or vice versa) is not only ineffective — it can alert victims they’re under attack. Such discovery may trigger a domino effect, jeopardizing attackers’ million-dollar 0-day 0-click vulnerabilities, full infrastructure, and target list.