CVE-2025-38352 (Part 1) - In-the-wild Android Kernel Vulnerability Analysis + PoC
December 21, 2025
Part 1 (This blog post) - In-the-wild Android Kernel Vulnerability Analysis + PoC
Part 2 - Extending The Race Window Without a Kernel Patch
Part 3 - Uncovering Chronomaly
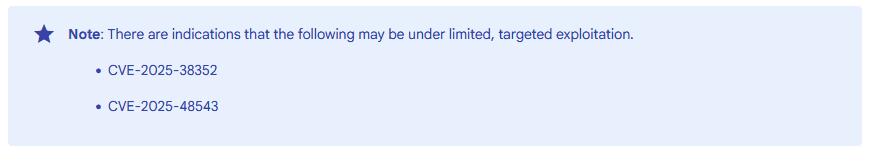
CVE-2025-38352 was a race condition use-after-free vulnerability in the Linux kernel's POSIX CPU timers implementation that was reported to have been under limited, targeted exploitation in the wild:
An analysis of this vulnerability was already posted by @streypaws. Their blog post does a good job explaining how POSIX CPU timers work, and the conditions under which this vulnerability can be triggered. You can find it here:
https://streypaws.github.io/posts/Race-Against-Time-in-the-Kernel-Clockwork/
Since their blog post does not provide a proof of concept program that triggers the vulnerability, I decided to turn my Sunday night into a night of learning and write it myself.
This blog post provides a glimpse into how I approach analysing and writing PoCs for vulnerabilities. It also goes to showcase how invaluable such an approach is for learning new things.